The Covid-19 pandemic is changing how we live our lives; however, there is one detail that is being overlooked – information security. In our rush to create work from home policies, it is important to remember that not all solutions are equal and that scams are on the rise. The last thing we need is a security incident or data breach on top of everything else. Here are a few things to consider:
Disaster Preparedness Protocol
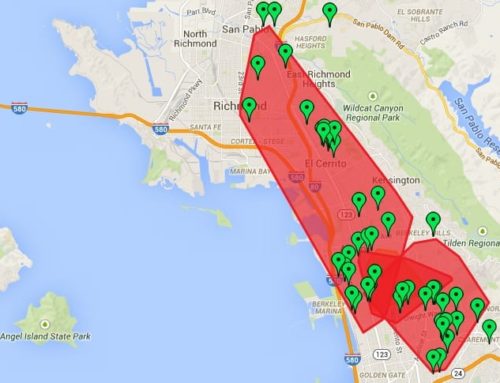
Living in northern California ourselves, the past few years have been trying. Wildfires, evacuations, and power shutoffs are becoming our new normal; this pandemic is just another disruption in which to cope. Due to our local disasters, our disaster preparedness protocols are more robust than many other areas of the country and even the world. Now is a perfect time to take a hard look at how you will address disasters and create a step by step protocol. Start here:
- Create a company contact list and make sure the information is current.
- Create a preparation checklist to ensure employees are ready for extended remote work.
- Draft a ‘work from home’ notice and link to your company’s HR policies, so people know what their options and boundaries are
- Plan for working from home.
Communicating Securely
SMS text messaging is not appropriate for sending sensitive office information, especially Protected Health Information (PHI). Alternatives are secure messaging platforms such as WhatsApp, Slack, and Teams. We always recommend that you involve your IT Provider in these decisions, and implement a solution that can be secured properly. The good news is that the tech industry is offering specials to help manage this global pandemic. In fact, Microsoft just announced the ability to acquire and use Teams for six (6) months free.
For the next six months, you can get the full version of Teams for free here
Use A Secure Remote Access Solution
Remote access is a program installed on your home computer or device that allows you to control your office computer. There is a wide variety of programs available, and while most can be secured, many are not without modifications to the settings. These are some things to help make a choice:
- Use a paid service
- Use a program that is installed on your computer
- Utilize 2-Factor Authentication
- Enable screen lock timeout with a password on both computers
- Avoid free built-in Remote Desktop Protocol or RDP without a VPN
VPN
VPN, or Virtual Private Network, is a secure channel directly to your office. While a VPN allows more ways into your office, they also open up more risks for hackers. It is important that your IT Provider set up a VPN and verify that all unnecessary open ports on the network are locked down. Proper configuration of the firewall and VPN is essential. Remember, clicking next, next, next, install is easy, but making and keeping it secure is different.
Another tip is to avoid free or public VPN apps. “Free” usually means that you are giving up your security or the security of the network you are removing into.
Risks and Concerns
Printing:
You can secure your physical office location and, therefore, anything you print within your office. Can you say the same about your home location(s)?
Saving Documents:
Saving documents on your computer should only be done if the computer you have at home is secured.
Email Programs:
Setting up work email on home computers or personal devices is risky unless that home device is secured to the same standard as your work machine. Leave email on your work computer and remote into it either with a program or VPN, rather than store it on your home device.
Email Scams:
This is a huge concern as the traffic on scams has increased exponentially in the last few weeks, and everyone desperate for the latest information. Be leery of emails claiming to be from WHO, Mayo Clinic, CDC, etc. The major news outlets are sharing legitimate information as fast as possible. Follow your local news stations, governments, municipalities, and law enforcement for accurate and timely information.
Computer Security:
If you absolutely need to store information on your home computer, remember the basics of computer security:
- Use a paid Antivirus
- Run your updates
- Patch your programs (Java, Adobe, Flash, IE, Firefox, Chrome, etc.)
- Utilize a Firewall
- Have Backups
- Use Strong Passwords
- Lock Your Screen
- Encrypt Whenever Possible
Cloud Solutions:
Programs that are accessible via a website are helpful; however, security and compliance are still concerns if the site is not set up properly or agreements aren’t in place. Again, engage your IT Provider to determine what is appropriate.
Telemedicine:
Video conference solutions are beneficial to continue care without in-person visits. These are available for many options, including comfort visits for orthodontists and treatment plan discussions for many specialties. Most people immediately think about FaceTime, but there are too many compliance issues and security concerns for this format.
There are options like Zoom and others; however, these formats are still not safe out of the box. They can be secure with setting changes. Please contact your IT Provider so they can alter the appropriate changes to make this form of communication convenient and secure. You don’t have to settle for one or the other.
This is new territory for many, but this too shall pass. It might pass like a kidney stone, but it will eventually pass.

Heading up the Compliance and Risk Management Division at ACS, Amy Wood consults with healthcare practitioners and Business Associate vendors, both before and after a Data Breach. She helps minimize the damage after a data breach and implements proactive compliance programs into existing workflows.
Amy also provides CE presentations to practices and clinics, dental associations, study clubs, and disability groups as well as to vendors and Business Associate practices. She can be reached at hipaa@acsdt.com